In a world where data never sleeps, every trace we leave online becomes a clue. OSINT — Open Source Intelligence — turns open information into power. From social media footprints to forgotten metadata, digital investigators learn to see what others overlook. No hacking, no intrusion — just the art of connecting dots in the endless sea of data.
Tag: technology
Social Engineering: How Hackers Trick You Without Touching a Line of Code
You don’t need malware to hack someone — just a good story. From Kevin Mitnick’s classic tricks to today’s AI-powered scams, social engineering proves one thing: people are still the weakest link in cybersecurity.
Kerberoasting: How It Works, How to Defend, and How to Minimize the Damage
Learn how Kerberoasting exploits Kerberos authentication in Active Directory, how it works, and what steps you can take to defend against it.
All-in on Cloud? Yes—but with your feet on the ground
Introduction Cloud technology is no longer a novelty — it’s the new normal. In recent years, more and more companies have been completing their shift from on-premise infrastructures to fully cloud-based environments. Not just for email or storage, but for core infrastructure, development environments, business data, and workflows. And yet, there’s still some hesitation. Some … Continue reading All-in on Cloud? Yes—but with your feet on the ground
Pass-the-Hash (PtH): Attack Technique and Complete Defenses
What is Pass-the-Hash? Pass-the-hash (PtH) is an attack technique that allows an attacker to authenticate to a remote system using the password hash, without the need for the password in plain text. It is particularly effective in Windows environments, where the NTLM authentication protocol allows authentication using static hashes. How the attack works Initial access … Continue reading Pass-the-Hash (PtH): Attack Technique and Complete Defenses
Tiering in Active Directory: Effective Strategy to Increase Security and Resiliency
Active Directory (AD) is the beating heart of identity and IT asset management in many organizations. Being a critical system, the AD frequently becomes the target of cyber attacks aimed at gaining elevated privileges or compromising entire corporate infrastructures. For this reason, tiering has become a critical approach to reducing risk and ensuring greater security … Continue reading Tiering in Active Directory: Effective Strategy to Increase Security and Resiliency
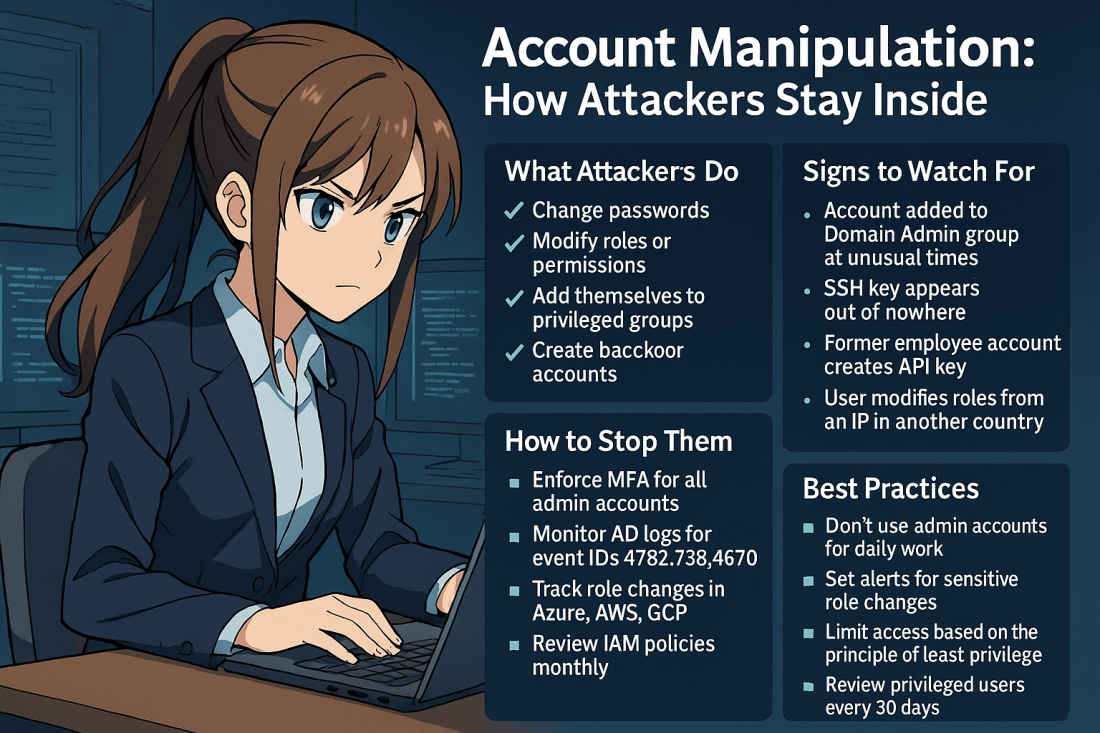
Account Manipulation: How Attackers Stay Inside Your Systems
Account manipulation is one of the stealthiest and most effective techniques used by threat actors to maintain or escalate access in compromised environments. Once inside, attackers often attempt to secure their foothold. They do this by modifying existing accounts. Another strategy is creating new ones that blend into your environment. This can include: Changing user … Continue reading Account Manipulation: How Attackers Stay Inside Your Systems
Windows Domain Name Service Remote Code Execution Vulnerability (CVE-2025-24064)
CVE-2025-24064 of March 11, 2025 highlights the possibility of executing malicious code on the network by exploiting the Use After Free vulnerability in the DNS server. The vulnerability shows the importance of allowing DNS updates only from trusted devices and therefore having only secure updates, preventing unrecognized devices from updating or adding their A record … Continue reading Windows Domain Name Service Remote Code Execution Vulnerability (CVE-2025-24064)
Migrating Your Windows Device from Active Directory to ENTRA ID
In a world where mobility is crucial, maintaining an AD joined computer can change from an asset to a burden. Modern users are constantly on the move. They do not rely on applications that need a constant remote connection. These users often manage a device tethered to an on-premise infrastructure. Instead of simplifying their daily … Continue reading Migrating Your Windows Device from Active Directory to ENTRA ID