Despite improvements in Microsoft cloud security, lateral movement in hybrid Azure AD environments is still viable in 2025 — and often undetected.
Tag: identity-security
Kerberoasting: How It Works, How to Defend, and How to Minimize the Damage
Learn how Kerberoasting exploits Kerberos authentication in Active Directory, how it works, and what steps you can take to defend against it.
Tiering in Active Directory: Effective Strategy to Increase Security and Resiliency
Active Directory (AD) is the beating heart of identity and IT asset management in many organizations. Being a critical system, the AD frequently becomes the target of cyber attacks aimed at gaining elevated privileges or compromising entire corporate infrastructures. For this reason, tiering has become a critical approach to reducing risk and ensuring greater security … Continue reading Tiering in Active Directory: Effective Strategy to Increase Security and Resiliency
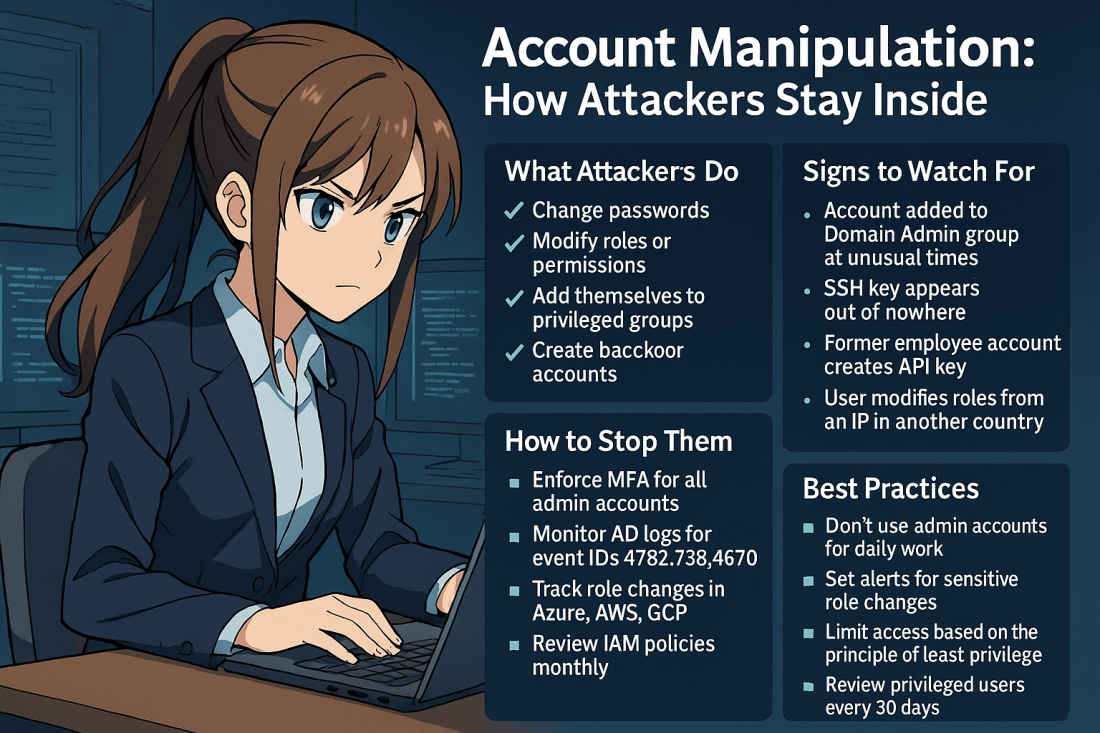
Account Manipulation: How Attackers Stay Inside Your Systems
Account manipulation is one of the stealthiest and most effective techniques used by threat actors to maintain or escalate access in compromised environments. Once inside, attackers often attempt to secure their foothold. They do this by modifying existing accounts. Another strategy is creating new ones that blend into your environment. This can include: Changing user … Continue reading Account Manipulation: How Attackers Stay Inside Your Systems
Steps to Migrate to New Authentication Techniques
Prepare the migration Beginning September 30, 2025, authentication techniques can't be managed in these legacy multi-factor authentication and self-service password reset policies. Before start the migration of the new authentication techniques you need to review the action configuration of: Multi-factor Authentication Policy S.S.P.R. Policy Review the legacy MFA policy Start by documenting which techniques are … Continue reading Steps to Migrate to New Authentication Techniques