In a world where data never sleeps, every trace we leave online becomes a clue. OSINT — Open Source Intelligence — turns open information into power. From social media footprints to forgotten metadata, digital investigators learn to see what others overlook. No hacking, no intrusion — just the art of connecting dots in the endless sea of data.
Tag: cyber-security
Social Engineering: How Hackers Trick You Without Touching a Line of Code
You don’t need malware to hack someone — just a good story. From Kevin Mitnick’s classic tricks to today’s AI-powered scams, social engineering proves one thing: people are still the weakest link in cybersecurity.
Lateral Movement in Azure AD: What Still Works in 2025
Despite improvements in Microsoft cloud security, lateral movement in hybrid Azure AD environments is still viable in 2025 — and often undetected.
Shadow Admins in Active Directory: The Privilege You Don’t See (Until It’s Too Late)
Shadow Admins are the privilege paths you’re not watching. These accounts don’t belong to Domain Admins, but they can take over your environment anyway — thanks to ACL misconfigurations, GPO access, or SIDHistory abuse. If you're only auditing group membership, you're already exposed.
Kerberoasting: How It Works, How to Defend, and How to Minimize the Damage
Learn how Kerberoasting exploits Kerberos authentication in Active Directory, how it works, and what steps you can take to defend against it.
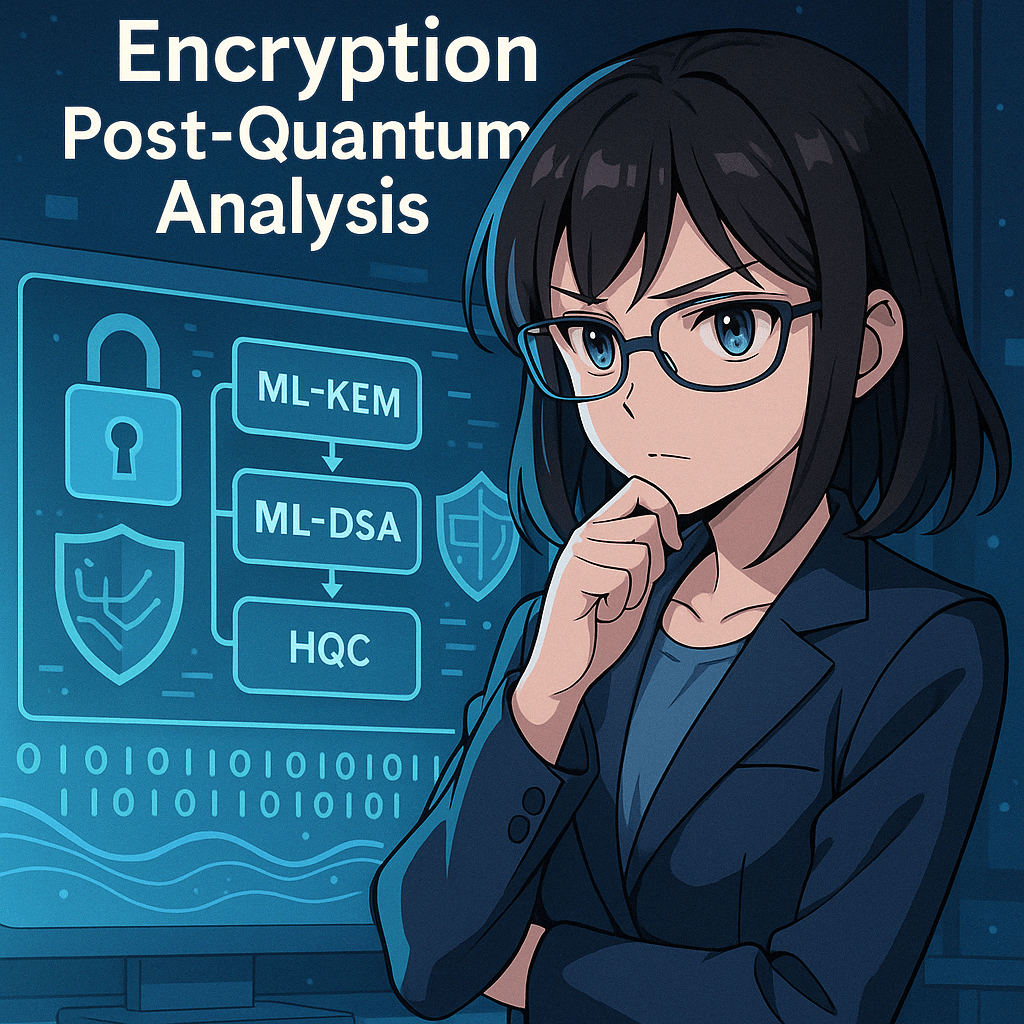
Quantum Computing and Cybersecurity: How Companies Can Prepare for the Quantum Wave
Introduction The tech world is quietly approaching a disruptive moment: the rise of quantum computing.This isn’t science fiction or something that only concerns physicists in lab coats. It's a technology that, once mature, could undermine the entire foundation of today’s cybersecurity—from encrypted emails to digital signatures, VPNs, and even blockchain. But why is that? And … Continue reading Quantum Computing and Cybersecurity: How Companies Can Prepare for the Quantum Wave
Pass-the-Hash (PtH): Attack Technique and Complete Defenses
What is Pass-the-Hash? Pass-the-hash (PtH) is an attack technique that allows an attacker to authenticate to a remote system using the password hash, without the need for the password in plain text. It is particularly effective in Windows environments, where the NTLM authentication protocol allows authentication using static hashes. How the attack works Initial access … Continue reading Pass-the-Hash (PtH): Attack Technique and Complete Defenses