In a world where data never sleeps, every trace we leave online becomes a clue. OSINT — Open Source Intelligence — turns open information into power. From social media footprints to forgotten metadata, digital investigators learn to see what others overlook. No hacking, no intrusion — just the art of connecting dots in the endless sea of data.
Category: Security Techniques
Practical security field notes covering how attacks work and how to stop them—techniques, detections, hardening, vulnerability analysis, plus OSINT and social engineering from a defensive mindset.
Social Engineering: How Hackers Trick You Without Touching a Line of Code
You don’t need malware to hack someone — just a good story. From Kevin Mitnick’s classic tricks to today’s AI-powered scams, social engineering proves one thing: people are still the weakest link in cybersecurity.
Kerberoasting: How It Works, How to Defend, and How to Minimize the Damage
Learn how Kerberoasting exploits Kerberos authentication in Active Directory, how it works, and what steps you can take to defend against it.
Pass-the-Hash (PtH): Attack Technique and Complete Defenses
What is Pass-the-Hash? Pass-the-hash (PtH) is an attack technique that allows an attacker to authenticate to a remote system using the password hash, without the need for the password in plain text. It is particularly effective in Windows environments, where the NTLM authentication protocol allows authentication using static hashes. How the attack works Initial access … Continue reading Pass-the-Hash (PtH): Attack Technique and Complete Defenses
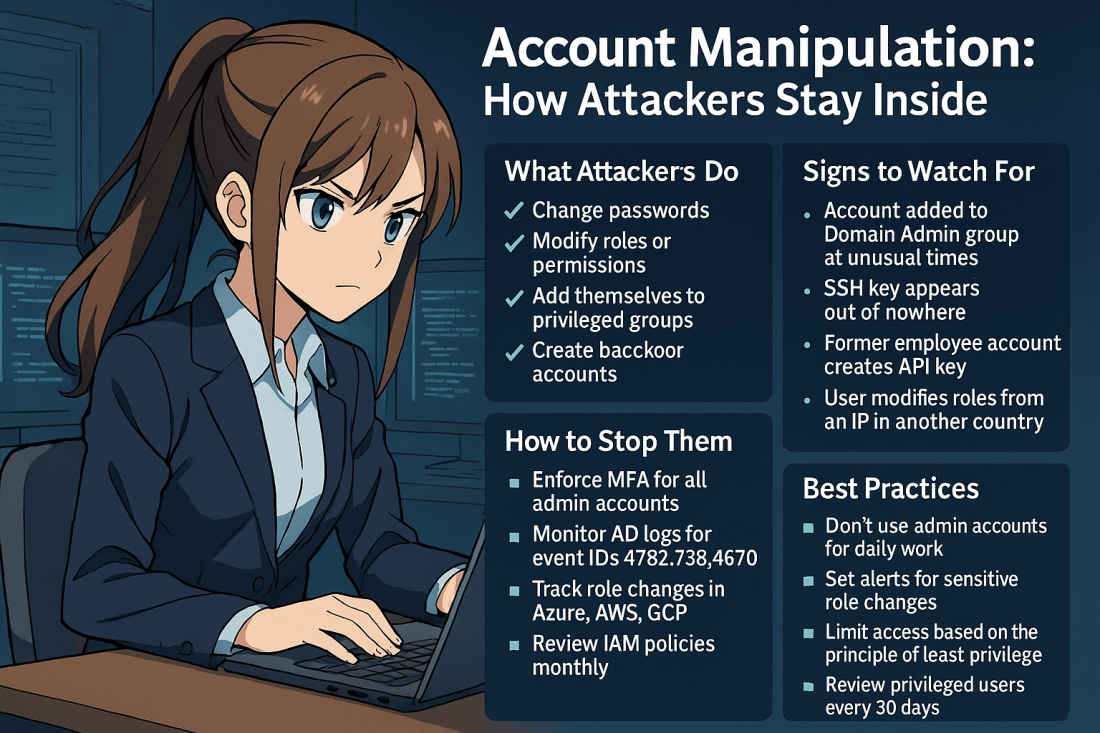
Account Manipulation: How Attackers Stay Inside Your Systems
Account manipulation is one of the stealthiest and most effective techniques used by threat actors to maintain or escalate access in compromised environments. Once inside, attackers often attempt to secure their foothold. They do this by modifying existing accounts. Another strategy is creating new ones that blend into your environment. This can include: Changing user … Continue reading Account Manipulation: How Attackers Stay Inside Your Systems
Windows Domain Name Service Remote Code Execution Vulnerability (CVE-2025-24064)
CVE-2025-24064 of March 11, 2025 highlights the possibility of executing malicious code on the network by exploiting the Use After Free vulnerability in the DNS server. The vulnerability shows the importance of allowing DNS updates only from trusted devices and therefore having only secure updates, preventing unrecognized devices from updating or adding their A record … Continue reading Windows Domain Name Service Remote Code Execution Vulnerability (CVE-2025-24064)
Secure Boot Vulnerability CVE-2023-24932: What You Need to Know
Secure Boot Security Feature Bypass Vulnerability (CVE-2023-24932) is a Security Vulnerability released on May 9, 2023. It allowed an attacker who successfully exploited this vulnerability to bypass Secure Boot on devices. To exploit the vulnerability, an attacker needs physical access or administrative rights to a target device. The attacker then install an affected boot policy. … Continue reading Secure Boot Vulnerability CVE-2023-24932: What You Need to Know
Windows LAPS: Transition from Legacy to Modern Password Management
The legacy Microsoft LAPS product is deprecated as of Windows 11 23 H2 and later. The installation of the legacy Microsoft LAPS MSI package is blocked on newer versions of the operating system. Microsoft will no longer consider code changes for the legacy Microsoft LAPS product. Microsoft recommends using Windows LAPS to manage local administrator … Continue reading Windows LAPS: Transition from Legacy to Modern Password Management