You don’t need malware to hack someone — just a good story. From Kevin Mitnick’s classic tricks to today’s AI-powered scams, social engineering proves one thing: people are still the weakest link in cybersecurity.
Category: Security Remediation
The Ghosts of Exchange: Hidden Permissions Lurking in Active Directory
Even after uninstalling Exchange, traces of its deep integration with Active Directory remain — powerful groups, lingering ACLs, legacy attributes, and automation leftovers. Whether Exchange is running or long gone, ignoring what it left behind could leave your domain exposed. Here's what you need to know (and clean up) before someone else does
Shadow Admins in Active Directory: The Privilege You Don’t See (Until It’s Too Late)
Shadow Admins are the privilege paths you’re not watching. These accounts don’t belong to Domain Admins, but they can take over your environment anyway — thanks to ACL misconfigurations, GPO access, or SIDHistory abuse. If you're only auditing group membership, you're already exposed.
Kerberoasting: How It Works, How to Defend, and How to Minimize the Damage
Learn how Kerberoasting exploits Kerberos authentication in Active Directory, how it works, and what steps you can take to defend against it.
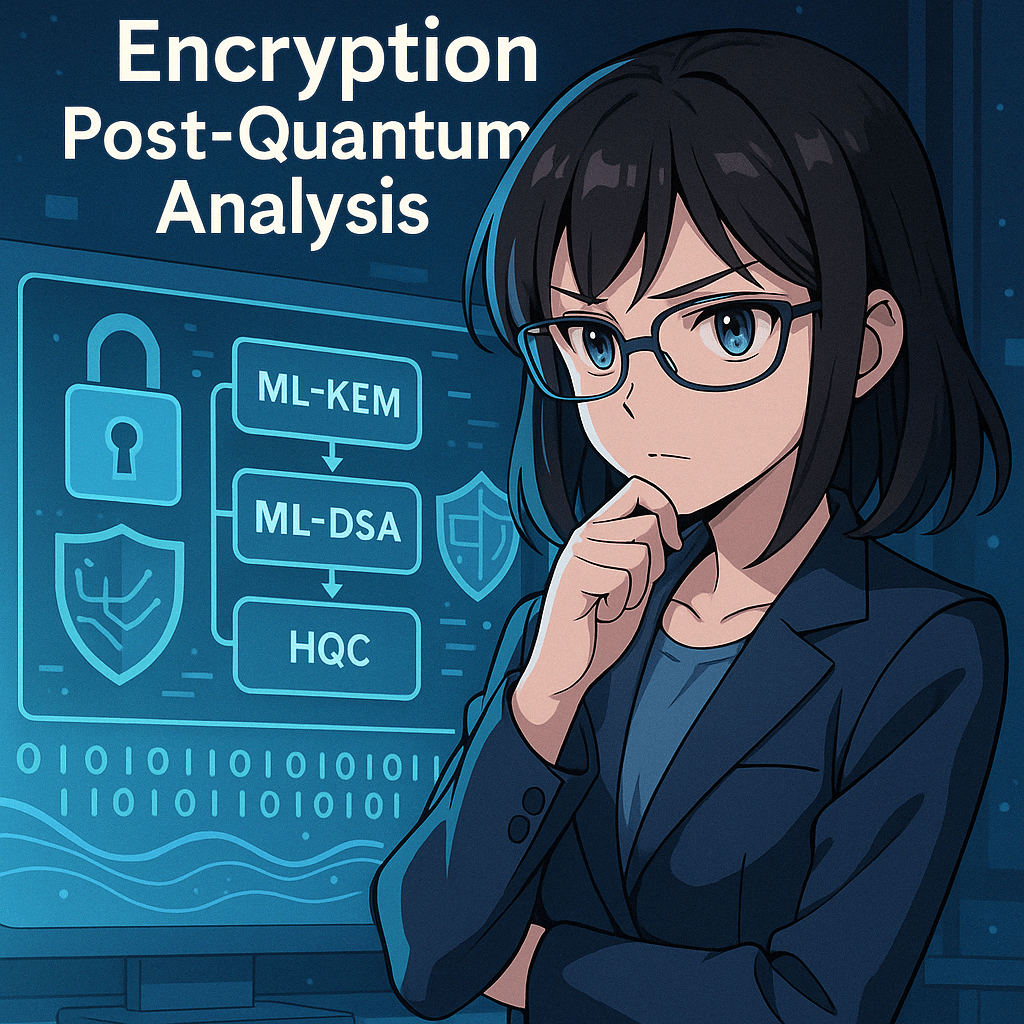
Quantum Computing and Cybersecurity: How Companies Can Prepare for the Quantum Wave
Introduction The tech world is quietly approaching a disruptive moment: the rise of quantum computing.This isn’t science fiction or something that only concerns physicists in lab coats. It's a technology that, once mature, could undermine the entire foundation of today’s cybersecurity—from encrypted emails to digital signatures, VPNs, and even blockchain. But why is that? And … Continue reading Quantum Computing and Cybersecurity: How Companies Can Prepare for the Quantum Wave
Pass-the-Hash (PtH): Attack Technique and Complete Defenses
What is Pass-the-Hash? Pass-the-hash (PtH) is an attack technique that allows an attacker to authenticate to a remote system using the password hash, without the need for the password in plain text. It is particularly effective in Windows environments, where the NTLM authentication protocol allows authentication using static hashes. How the attack works Initial access … Continue reading Pass-the-Hash (PtH): Attack Technique and Complete Defenses
Tiering in Active Directory: Effective Strategy to Increase Security and Resiliency
Active Directory (AD) is the beating heart of identity and IT asset management in many organizations. Being a critical system, the AD frequently becomes the target of cyber attacks aimed at gaining elevated privileges or compromising entire corporate infrastructures. For this reason, tiering has become a critical approach to reducing risk and ensuring greater security … Continue reading Tiering in Active Directory: Effective Strategy to Increase Security and Resiliency
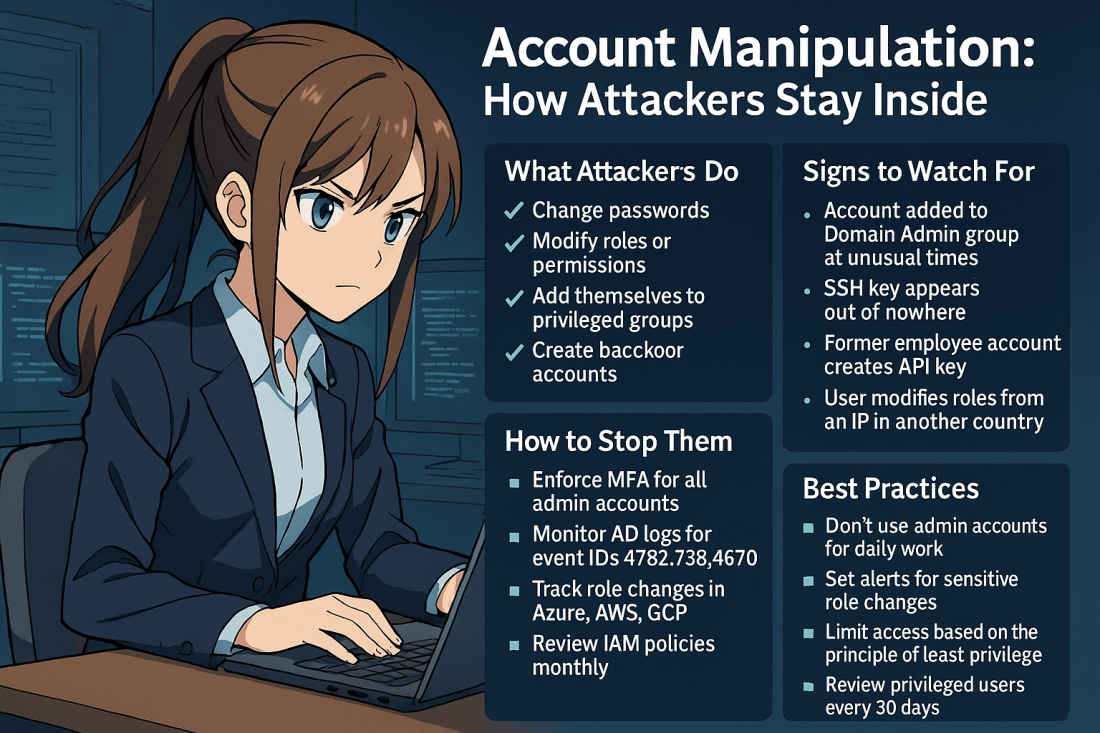
Account Manipulation: How Attackers Stay Inside Your Systems
Account manipulation is one of the stealthiest and most effective techniques used by threat actors to maintain or escalate access in compromised environments. Once inside, attackers often attempt to secure their foothold. They do this by modifying existing accounts. Another strategy is creating new ones that blend into your environment. This can include: Changing user … Continue reading Account Manipulation: How Attackers Stay Inside Your Systems
Secure Boot Vulnerability CVE-2023-24932: What You Need to Know
Secure Boot Security Feature Bypass Vulnerability (CVE-2023-24932) is a Security Vulnerability released on May 9, 2023. It allowed an attacker who successfully exploited this vulnerability to bypass Secure Boot on devices. To exploit the vulnerability, an attacker needs physical access or administrative rights to a target device. The attacker then install an affected boot policy. … Continue reading Secure Boot Vulnerability CVE-2023-24932: What You Need to Know