Active Directory (AD) is the beating heart of identity and IT asset management in many organizations. Being a critical system, the AD frequently becomes the target of cyber attacks aimed at gaining elevated privileges or compromising entire corporate infrastructures. For this reason, tiering has become a critical approach to reducing risk and ensuring greater security and resilience.
What is Tiering in Active Directory?
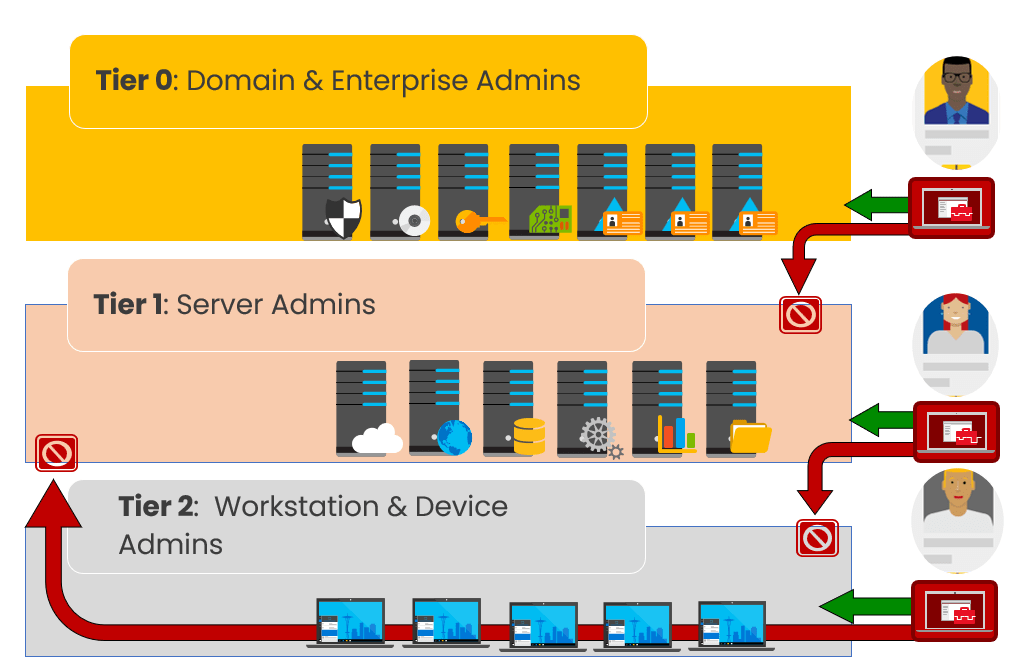
Tiering is a methodology that divides resources and accounts into separate privilege levels, preventing the uncontrolled spread of administrative permissions and significantly reducing the attack surface. The main goal is to contain the potential damage resulting from a compromised account.
The key principles of tiering are:
- Strict separation of administrative resources and accounts.
- Minimizing assigned privileges.
- Strict access control between the different levels.
Why implement tiering?
Implementing tiering allows you to:
- Limit the lateral movement of any attackers.
- Reduce your attack surface with asset segmentation.
- Prevent privilege escalation, that is, prevent a compromised user from obtaining higher or critical credentials.
- Facilitate security management through clear and separate policies.
Description of the levels (Tiers)
Tier 0 (Critical Level)
It includes the critical resources that control the infrastructure:
- Domain Controllers and critical servers (Azure AD Connect, AD FS).
- High-level administrative accounts (Enterprise Admins, Domain Admins).
- Safety management systems (e.g. SIEM, PAM).
Tier 1 (Intermediate Level)
It includes important but non-vital IT resources:
- Application servers.
- SQL databases and important enterprise servers.
- Application management systems.
Tier 2 (Entry-level level)
Includes general resources and standard user seats:
- Users’ PCs and laptops.
- General systems and non-critical applications.

Implementing tiering step by step
Here’s a practical path to tiering:
1. Asset Analysis and Classification
- Carry out a detailed inventory of assets and accounts.
- Classify each asset according to the level of risk (Tier 0, Tier 1, Tier 2).
2. Precise Definition of Privileges
- Assign privileges that are consistent with the defined levels.
- Strictly limit inter-tier access.
3. Creating and enforcing policies
- Use Group Policy Objects (GPOs) to enforce precise security rules.
- Continuously monitor access and administrative activities.
4. Administrative and managerial separation
- Use separate administrative accounts for each level.
- Use dedicated administrative workstations (Privileged Access Workstations – PAWs) to manage Tier 0.
Tiering tools and best practices
To further strengthen tiering, specific tools should be used:
- Privileged Access Workstations (PAWs): Workstations dedicated exclusively to the management of critical systems (Tier 0).
- Just-In-Time (JIT) and Just-Enough-Administration (JEA): Approaches to grant privileges only when strictly necessary.
- Privileged Access Management (PAM): Strumenti come Microsoft Identity Manager (MIM), CyberArk o BeyondTrust.
- Microsoft LAPS (Local Administrator Password Solution): Allows secure and centralized management of local passwords.
- Microsoft Defender for Identity: A monitoring tool to detect suspicious activity in AD.
Common Mistakes to Avoid When Implementing Tiering
When implementing tiering, there are a few common mistakes that you should definitely avoid:
- Confuse roles and tiers: Don’t assign accounts to multiple tiers at once.
- Misuse of administrative accounts: Avoid using highly privileged accounts on standard (Tier 2) locations.
- Lack of monitoring and auditing: Tiering is not a substitute for the need for continuous monitoring of administrative activities.
Conclusion
Implementing tiering in Active Directory is now a critical best practice for any organization that takes cybersecurity seriously. Through clear asset segmentation and strict access management, you can significantly reduce the risk of compromise and ensure rapid recovery in the event of an incident.
Taking a structured approach to tiering today is not only a strategic choice, but an obligation to protect your most valuable business assets.